Visual analytics for Anomaly Detection in IοT networks
8/3/2021
Internet of things (IoT) is defined as the embodiment of various physical devices or objects to Internet. Due to the frequency of utilization of such connected devices in our daily activities and the unattended and open operations of the network, numerous inherent security challenges in IoT systems have emerged. Treatment of these challenges could be achieved both via using anomaly detection algorithms and monitoring of different types of data produced by devices within an IoT network via visual analytics techniques.
Because of the fact that human domain expertise and computational results can differ from each other, visual analytics can be used to integrate human knowledge with analytics results to solve this issue. Visual analytics anomaly detection has been mainly based on statistical, machine learning and deep learning techniques. There are some special challenges in this field to be resolved, such as the unstable boundary between normal and abnormal cases, and the difficulty of collecting annotated data with exact labels. Generally, the deployed anomaly detection models should on the one hand take into account the fact that there are not clear bounds in distinguishing normal and abnormal patterns and on the other hand not only be based on users’ feedback in analysis stage [1]. More specifically, visual analytics should find answers in a range of problems such as the interpretation of multidimensional data from IoT sensors and devices, the creation of accurate normal behavioral models from data, the detection of anomalous points and interpretation of abnormal events [2].
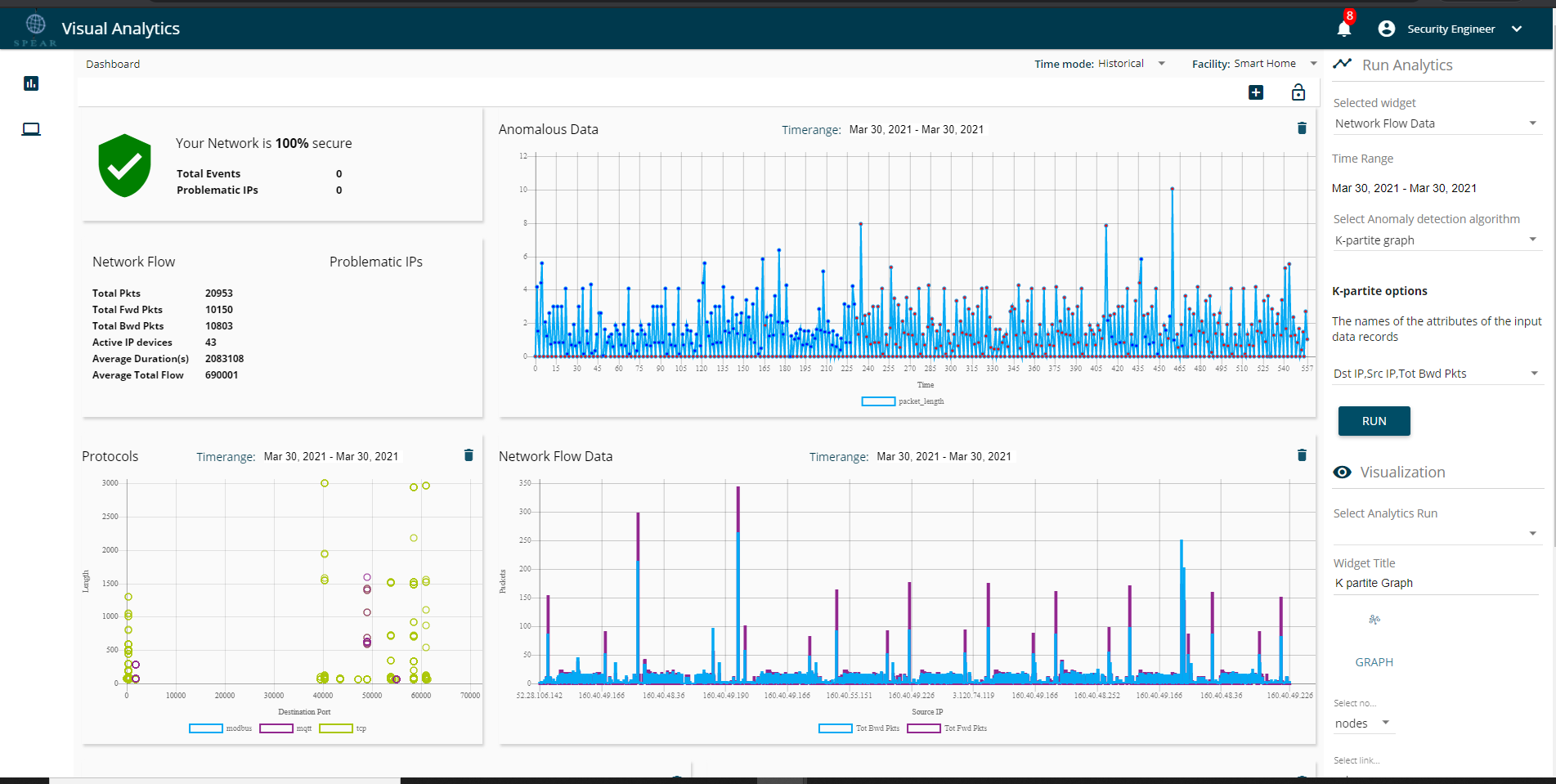
To face those problems, numerous approaches have been recommended. Some examples are the affection of later model time epochs by real-time data and the integration of user feedback without the re-computation of anomaly detection model based on historical pattern of data [3]. Moreover, it is essential that the data representation should be interpretable in order to assist human interaction with the system [1].SPEAR visual analytics techniques for anomaly detection aim to respond to the aforementioned challenges by monitoring data from many different sources and devices belonging to a smart infrastructure. Specifically, visual analytics tool utilizes data sources such as network traffic data (network flow statistics, deep packet inspection data) and operational data of an infrastructure IoT devices (e.g. battery data, PV data and smart meters’ data in the case of a smart home IoT network).
Visual analytics module in SPEAR system, apart from numerous ways of data visualization, has special functionalities for anomaly detection. This special visualization and analytics module not only is based in data context and comprises visual data comparisons and correlations, but also offers real-time detection and visual annotation of abnormalities, in order to assist users to give accurate feedback. The capacity of system to allow users to record the results and monitor data analysis progress undeniably is an important requirement for the system. The user feedback is essential, so that new anomalous patterns corresponding to cyber-attacks are discovered and the detection capability of intrusion detection systems that operate in parallel is enhanced with new knowledge [1]. SPEAR security infrastructure utilizes interactive visualization charts to monitor real-time data and to detect anomalies, possibly related with cyber-attacks, through a variety of deep learning algorithms. The deployed models have been trained to learn the normal patterns from different data sources, in order to detect unusual behaviors that significantly deviate from expected operation. If the maximum reconstruction error of a data instance overcomes a calculated threshold, this is being labeled as anomalous.
The other module for Visual analytics is the GTM module. The purpose of GTM is to quantify the severity of the various security events and calculate a reputation value for each asset of the smart-grid. This quantification intends to measure the impact of the detected anomaly as well as each asset individually.
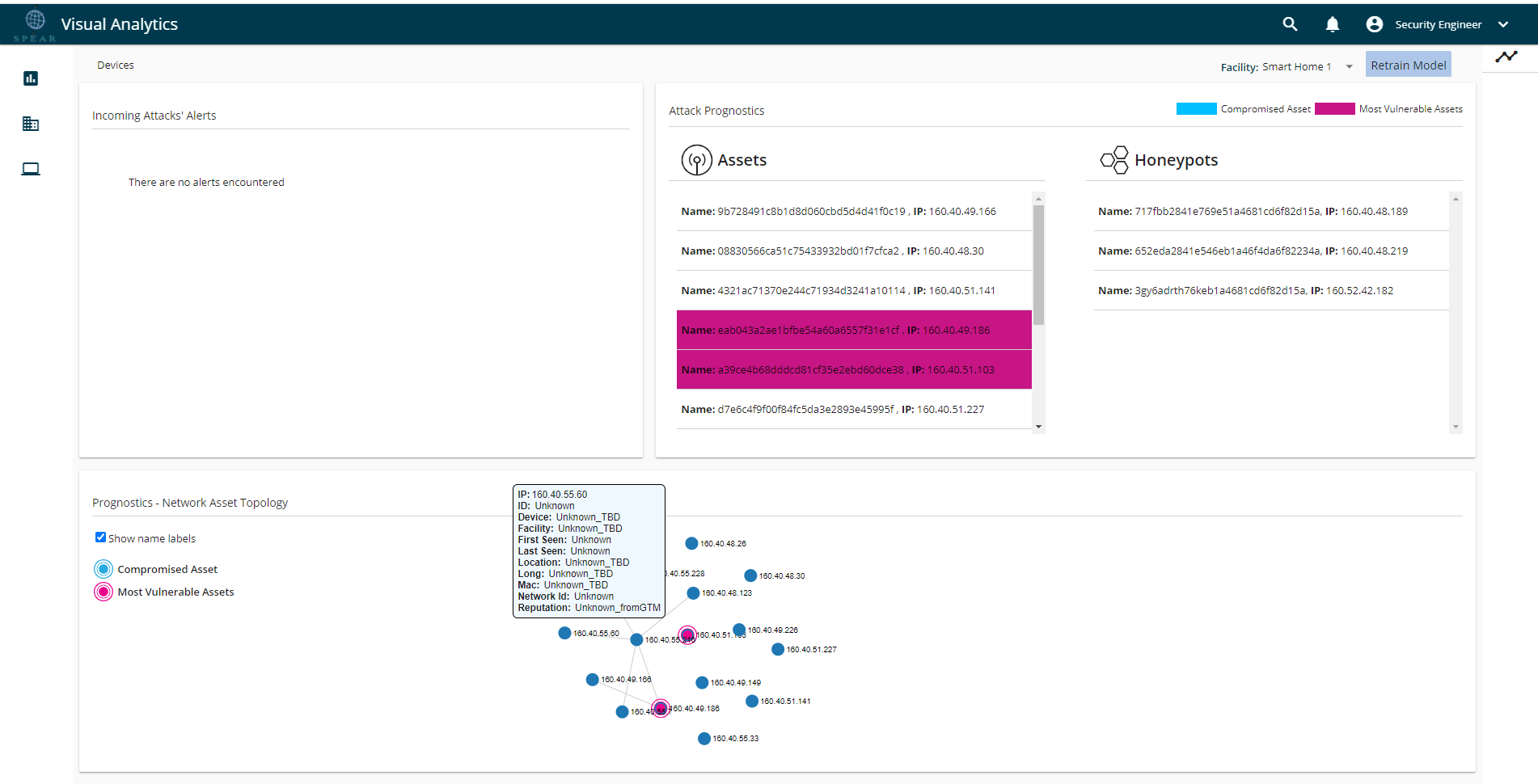
In conclusion, visual analytics is an anomaly detection and visualization system tool with trust management functionality. Additional capabilities include security events creation, display of network topology with information about all the assets, periodic remote notifications to end users through Instant Message (IM) application regarding the status of the network and potential anomalies. One special capability of the system is the interaction with the user to receive feedback, in order to link anomalous instances indicated by the anomaly detection models with cyber-attacks.
References
- N. Cao, C. Lin, Q. Zhu, Y.-R. Lin, X. Teng and X. Wen, "Voila: Visual Anomaly Detection and Monitoring with Streaming Spatiotemporal Data," IEEE transactions on visualization and computer graphics, vol. 24, no. 1, pp. 23-33, 2017.
- M. Riveiro, M. Lebram and M. Elmer, "Anomaly detection for road traffic: A visual analytics framework," IEEE Transactions on Intelligent Transportation Systems, vol. 18, no. 8, pp. 2260-2270, 2017.
- A. Saad and N. Sisworahardjo, "Data analytics-based anomaly detection in smart distribution network," in 2017 International Conference on High Voltage Engineering and Power Systems (ICHVEPS), IEEE, 2017, pp. 1-5.