Secure and Private Smart Grids: The SPEAR Architecture
4/10/2020
The power grid consists one of the so-called “critical infrastructures” that are essential to vital societal functions. The transformation of conventional power grids to the smart grids of the future has introduced numerous benefits, including flexibility, pervasive control, and utilisation of resources, but also created significant challenges that risk the operation of the power grid and, therefore, can cause cascading effects to essential societal sectors.
An unavoidable effect caused by the deployment of Information and Communication Technologies (ICT) in the power grid is the increasing attack surface of the critical infrastructure, which is now exposed to a growing number of (known and unknown) threats. As a result, efficient and dynamic systems are needed to tackle the susceptibilities introduced by the digitalisation of the power grid, while the societies and the economies benefit from the resiliency and efficiency of the modern smart grid.
The SPEAR solution, proposed by this project, aims to provide the ability to energy operators to timely detect cyberthreats against their infrastructures, considering in parallel privacy-related issues and the collection of forensic-related data. Moreover, SPEAR intends to enhance situational awareness of energy-related stakeholders by establishing an anonymous repository of incidents. In a nutshell, the novelties of SPEAR are compiled in the following pillars:
- Intrusion detection using big data and visual analytics
- Honeypots
- Network forensics
- Cybersecurity information sharing
The above technology pillars are the basis of the SPEAR architecture, which is illustrated in the figure bellow. In particular, the SPEAR architecture is analysed to the following frameworks:
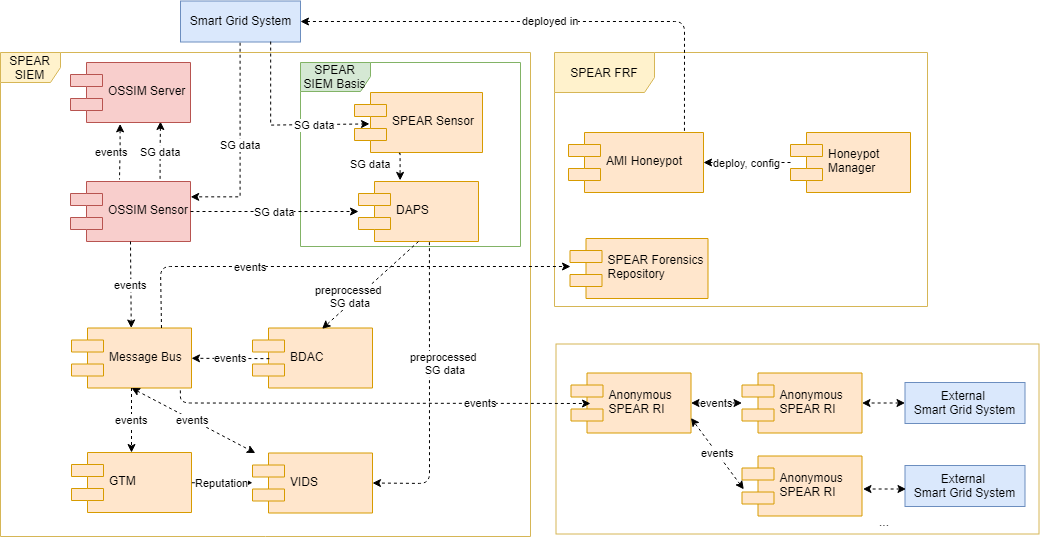
SPEAR SIEM
The Security Information and Event Management (SIEM) system is the major framework of the SPEAR architecture that is composed of a) AlienVault OSSIM, b) SPEAR SIEM Basis, c) Big Data Analytics Component (BDAC), d) Visual-aided Intrusion Detection System (V-IDS) and e) Grid-Trusted Module (GTM). In more detail, AlienVault OSSIM collects network traffic from the infrastructure and focuses on signature-based anomaly detection, whilst SIEM Basis captures and pre-processes network traffic and operational data (e.g., various electricity measurements) to be received by other components further processing. BDAC provides User and Entity Behaviour Analysis (UEBA) by employing machine learning and deep learning techniques to analyse network traffic and operational data to detect possible anomalies. Moreover, GTM indicates how dangerous each asset is for the business operations by assigning a corresponding reputation value, which is calculated by assessing security events and static data about the infrastructure, combined with fuzzy logic techniques. Finally, V-IDS depicts the security events generated by all SPEAR components and further facilitates the detection of anomalies by providing advanced visual analytics that can be used by the security administrator or facility operator to detect and indicate additional security events that were not detected automatically.
SPEAR FRF
The Forensic Readiness Framework (FRF) provides the necessary tools and procedures to enable forensic readiness for smart grid operators by employing the Camunda BPM tool as well as privacy awareness compliant to the EU legislation by supporting a Privacy Impact Assessment (PIA). FRF consists of three main components, namely a) Forensic Repository (FR), b) AMI Honeypots and c) Honeypot Manager. In more detail, FR is responsible for collecting information and evidence from the infrastructure that can be used for legal purposes, while focusing on user privacy and the requirement that the evidences should remain unforged in order to be valid. AMI Honeypots are software components that aim to lure cyber-attackers by imitating real devices of the smart grid ecosystem. Their goal is twofold: i) to hide the real assets and ii) collect intelligence about the malicious activities. SPEAR Honeypots (based on Cowire and Conpot) can emulate various communication protocols, including Modbus, BACnet, GOOSE/MMS and SSH amongst others. The honeypots provided by the SPEAR solution are further enhanced by Generative Adversarial Networks (GANs), an AI solution that enables honeypots to be trained by network traffic data in order to generate more realistic responses, thus being more convincing. Finally, the Honeypot Manager acts as the orchestrator of those honeypots and a decision support system that applies a game theoretic model to calculate the optimal deployment of honeypots in the infrastructure, based on a cost-benefit analysis.
SPEAR RI
The Repository of Incidents (RI) provides a common communication channel for all energy-related stakeholders that adopt the SPEAR solution across Europe to exchange anonymously information regarding cybersecurity incidents without exposing their identity. RI (based on MISP) ensures privacy and anonymity of the participating organisations by applying various anonymization techniques to new security events received by SPEAR SIEM, before being published, including k-anonymity, i-diversity, t-closeness and pseudo-anonymisation.